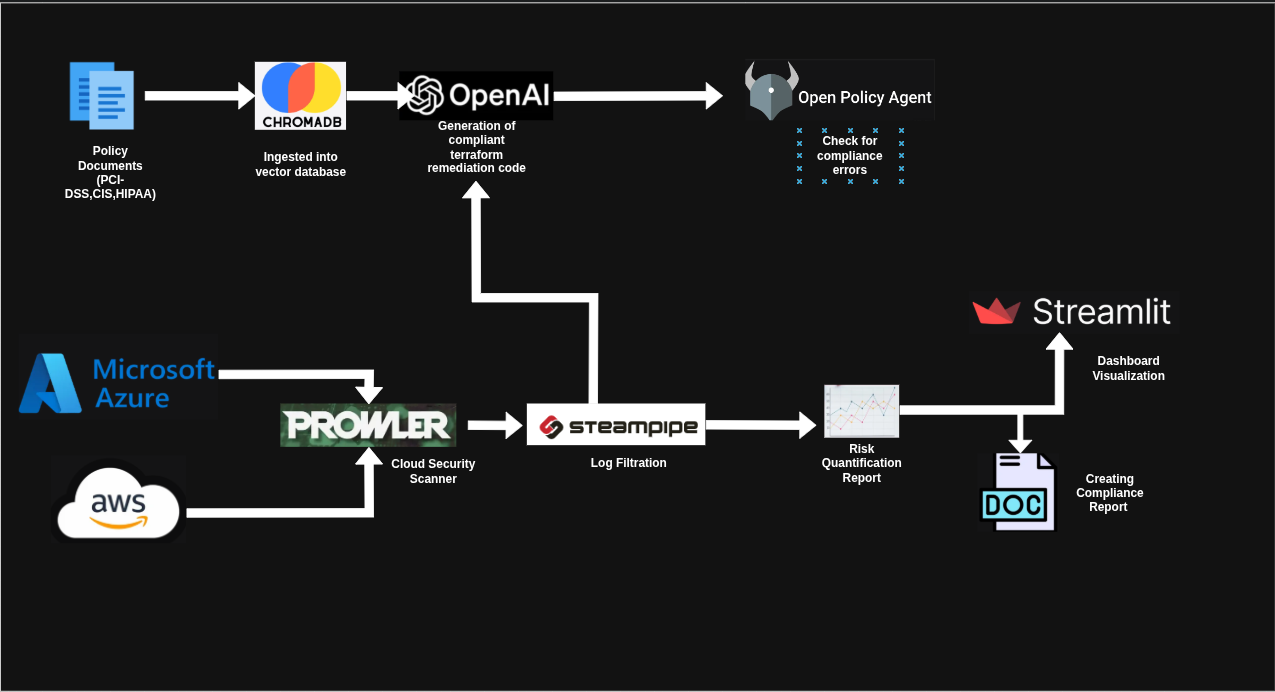
Multi-Cloud GRC Compliance & Remediation Engine
Audit prep usually means an engineering team burning weeks manually going through spreadsheets. I wanted to see how much of that pain could be killed with automation. Turns out: most of it.
This engine scans 94 CIS controls, figures out what's broken in your cloud, generates the Terraform to fix it, and validates the fix before it touches production. It turns a week-long compliance nightmare into an afternoon task.